Multiple Signatures and Handbook Grades
Keeping your company protected doesn’t end on an employee’s first day. Over time, laws, regulations, and best-practices change and your handbook changes right alongside. We recently made it easy to keep employees informed of those changes but sometimes the changes are so big that you want to collect new signatures. Or maybe you added your code of conduct to make it easy to keep updated, and that code gets signed off every year. We’ve heard from you that these are very real situations and our latest update addresses them.
This also forced a change to the documentation center. The new documentation center’s purpose is to communicate the following, clearly and efficiently, on your behalf: Am I current? Am I doing everything I can to keep the company protected? If not, where (or who) are the risks?
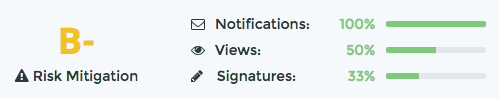
Every employee now has a risk rating, and all those ratings contribute to an overall risk mitigation grade. If everyone has signed the latest signature round, you get an A+. If employees haven’t signed, you get points when you’ve made sure they know about the handbook and when they view it.
Look for the dashboard to get improved and tweaked over time!